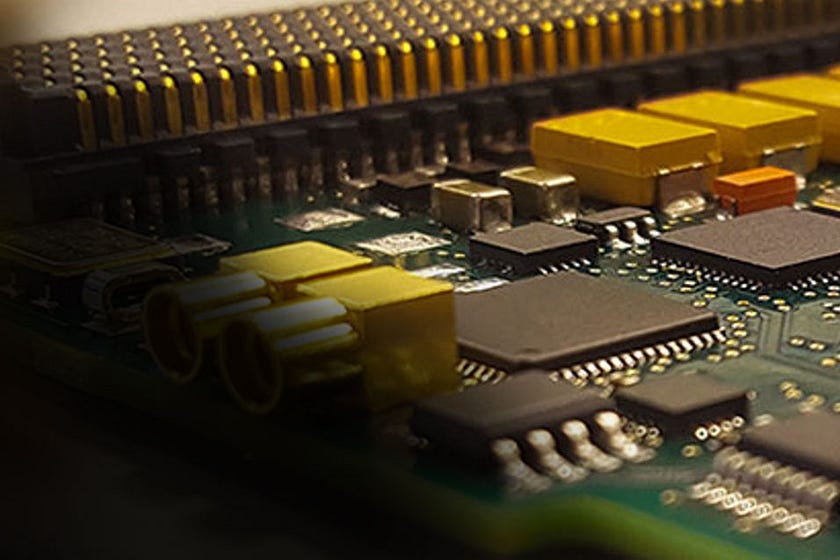
Navigating the Complex Terrain of Hardware Design Security Challenges
In the ever-evolving landscape of technology, hardware design security has become an indispensable concern. As the foundation upon which software and systems are built, hardware must be safeguarded against an array of security threats.
1. Supply Chain Vulnerabilities:
The hardware supply chain is intricate, involving numerous suppliers and subcontractors. This complexity creates opportunities for malicious actors to introduce counterfeit components, backdoors, or other vulnerabilities during the manufacturing process. Verifying the authenticity and integrity of hardware components throughout the supply chain is a formidable challenge.
2. Hardware Trojans:
Hardware Trojans are malicious alterations or additions to a chip’s design that can remain dormant until activated by a trigger condition. These insidious threats can compromise the security and functionality of a device. Detecting hardware Trojans, especially those carefully crafted to evade detection, is a significant challenge for designers.
3. Side-Channel Attacks:
Protecting against these attacks requires sophisticated countermeasures, including the use of secure hardware modules and encryption techniques.
4. Intellectual Property Theft:
Hardware intellectual property (IP) is highly valuable, and its theft poses significant security risks. Malicious actors may attempt to reverse engineer or steal proprietary hardware designs, leading to the creation of counterfeit products or vulnerabilities in legitimate ones.
5. Design Complexity:
Modern hardware designs are exceptionally complex, making it challenging to ensure that every component is secure. As designs grow in size and intricacy, identifying and mitigating potential vulnerabilities becomes increasingly difficult.
6. Lack of Standardization:
The absence of standardized security practices in hardware design contributes to inconsistencies in security implementations.
7. Post-Deployment Security:
Hardware security isn’t limited to the design phase; it must extend throughout a device’s lifecycle. Ensuring that hardware remains secure after deployment, through regular updates and patching, is a continuous challenge.
8. Design security issues in hardware:
Testing hardware for vulnerabilities is a complex and resource-intensive process. Developing effective testing methodologies and tools that can uncover both known and novel threats is a persistent challenge.
In conclusion, hardware design security is a multifaceted challenge that spans the entire lifecycle of a device, from its conception to its eventual retirement. As technology continues to advance, hardware designers must remain vigilant, continuously adapting and developing innovative solutions to protect against an ever-evolving landscape of security threats.
Comments
Post a Comment